OpenShift Origin
Over several post I ‘ll show how to install OpenShift over Fedora 19.
This is the diagram:
1 “broker” machine with at least 1Gb of RAM y 10 Gb of HDD (I’ll do it over a virtual machine)
1 “node1” machine with at least 1Gb of RAM y 30 Gb of HDD (I’ll do it over a virtual machine too)
It can also be done on a single machine, but to better understand the behavior of each component is best done separately.
Let’s start.
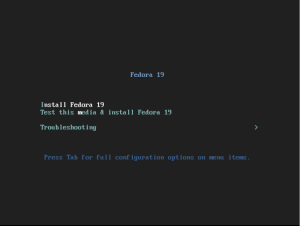
Operating System installation
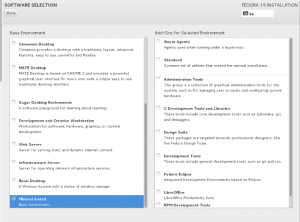
We must install Fedora 19 on both machines.
at software selection, we choose minimal install.
Hosts Configurations
-
Systems used : broker and node1
Let’s update both systems after the installation
yum update -y systemctl reboot
To perform an installation without hassle, the first thing we do is set OpenShift Origin v3 repositories. We assume that we are “root” on both hosts.
cat <<EOF> /etc/yum.repos.d/openshift.repo [openshift-origin] name=openshift-origin baseurl=http://mirror.openshift.com/pub/origin-server/release/3/fedora-19/packages/x86_64/ gpgcheck=0 enabled=1 [openshift-origin-deps] name=openshift-origin-deps baseurl=http://mirror.openshift.com/pub/origin-server/release/3/fedora-19/dependencies/x86_64/ gpgcheck=0 enabled=1 EOF
It’s important that all systems are synchronized, so let’s install ntp and synchronize with a network clock.
yum install -y ntpdate ntp ntpdate clock.redhat.com systemctl enable ntpd.service systemctl start ntpd.service
Let’s remove firewalld for simplified management, and install system-config-firewall.
yum remove -y firewalld yum install -y system-config-firewall
DNS configuration
-
Systems used: broker
First let’s install bind and bind-utils packages, which provide tools for configuring the name server.
yum install -y bind bind-utils
The broker machine will be responsible to manage all nodes, their namespaces, etc. The broker must have access to DNS to modify the entries, so let’s securize the DNS server with DNSSEC.
To avoid a lot of typing, let’s use a few system variables. I’ll use as domain “dmartin.es”, you can use the one you want.
domain=dmartin.es
keyfile=/var/named/${domain}.key
Let’s create DNSSEC key pair, and save private key value on a KEY variable.
cd /var/named
dnssec-keygen -a HMAC-MD5 -b 512 -n USER -r /dev/urandom ${domain}
KEY="$(grep Key: K${domain}*.private | cut -d ' ' -f 2)"
echo $KEY
We must create another key to allow access on DNS server to startup script.
rndc-confgen -a -r /dev/urandom
Let’s configure the owner and the file permissions. Also let’s restore the SELinux context (yes, Enforcing mode will be enabled)
chown -v root:named /etc/rndc.key chmod -v 640 /etc/rndc.key restorecon -v /etc/rndc.* /etc/named.*
A forwarder configuration must be created to allow queries to other DNS (for a external resolution)
echo "forwarders { 8.8.8.8; 8.8.4.4; } ;" >> /var/named/forwarders.conf
restorecon -v /var/named/forwarders.conf
chmod -v 640 /var/named/forwarders.conf
We create the dynamic resolution directory, and let’s create the config file.
mkdir /var/named/dynamic
cat << EOF >/var/named/dynamic/${domain}.db
\$ORIGIN .
\$TTL 1 ; 1 seconds (for testing only)
${domain} IN SOA ns1.${domain}. hostmaster.${domain}. (
2014090100 ; serial
60 ; refresh (1 minute)
15 ; retry (15 seconds)
1800 ; expire (30 minutes)
10 ; minimum (10 seconds)
)
NS ns1.${domain}.
MX 10 mail.${domain}.
\$ORIGIN ${domain}.
ns1 A 127.0.0.1
EOF
Let’s verify content
cat /var/named/dynamic/${domain}.db
$ORIGIN .
$TTL 1 ; 1 seconds (for testing only)
dmartin.es IN SOA ns1.dmartin.es. hostmaster.dmartin.es. (
2014090100 ; serial
60 ; refresh (1 minute)
15 ; retry (15 seconds)
1800 ; expire (30 minutes)
10 ; minimum (10 seconds)
)
NS ns1.dmartin.es.
MX 10 mail.dmartin.es.
$ORIGIN dmartin.es.
ns1 A 127.0.0.1
We install DNSSEC key for the domain, and update the owner and the SELinux context.
cat < /var/named/${domain}.key
key ${domain} {
algorithm HMAC-MD5;
secret "${KEY}";
};
EOF
chown -Rv named:named /var/named
restorecon -rv /var/named
Now, the BIND main config file.
cat < /etc/named.conf
// named.conf
//
// Provided by Red Hat bind package to configure the ISC BIND named(8) DNS
// server as a caching only nameserver (as a localhost DNS resolver only).
//
// See /usr/share/doc/bind*/sample/ for example named configuration files.
//
options {
listen-on port 53 { any; };
directory "/var/named";
dump-file "/var/named/data/cache_dump.db";
statistics-file "/var/named/data/named_stats.txt";
memstatistics-file "/var/named/data/named_mem_stats.txt";
allow-query { any; };
recursion yes;
/* Path to ISC DLV key */
bindkeys-file "/etc/named.iscdlv.key";
// set forwarding to the next nearest server (from DHCP response
forward only;
include "forwarders.conf";
};
logging {
channel default_debug {
file "data/named.run";
severity dynamic;
};
};
// use the default rndc key
include "/etc/rndc.key";
controls {
inet 127.0.0.1 port 953
allow { 127.0.0.1; } keys { "rndc-key"; };
};
include "/etc/named.rfc1912.zones";
include "${domain}.key";
zone "${domain}" IN {
type master;
file "dynamic/${domain}.db";
allow-update { key ${domain} ; } ;
};
EOF
chown -v root:named /etc/named.conf
restorecon -v /etc/named.conf
Let’s configure firewall and enable DNS service
systemctl start iptables systemctl enable iptables lokkit --service=dns systemctl start named
Let’s add broker to DNS
# nsupdate -k ${keyfile}
> server 127.0.0.1
> update add broker.dmartin.es 180 A 10.10.10.2
> send
#dig @127.0.0.1 broker.dmartin.es
Now is the time to configure network.
If we have static configuration, only we need to point to our DNS server.
I’ll show how to configure a DHCP configuration, and how to avoid that DHCP server gives us another DNS server and another domain.
cat <<EOF> /etc/sysconfig/network-scripts/ifcfg-eth0 NAME="eth0" TYPE="Ethernet" BOOTPROTO="dhcp" PEERDNS="no" DNS1="127.0.0.1" EOF
Finally let’s modify hostname.
hostnamectl broker.dmartin.es cat /etc/hostname
In the next post, let’s configure MongoDB database and ActiveMQ messaging broker. It’s available here.
See you soon.